70-483 Notes
A while ago I passed the 70-483 exam and thought I might share some of my notes, which I think are the most takeaways from the learning material. The exam itself was fair, but as almost every knowledge test it had some very specific questions such as name of the methods on interfaces (e.g. CompareTo vs Compare on IComparable and IComparer respectively).
1. Parallel LINQ queries does not guarantee preserved order, need to add the AsOrdered() characteristic. It might be quicker than sequential linq query, but it’s not deterministic, need to be tested. Example PLINQ queries:
var orderedCities2 = (from city in cities.AsParallel().AsOrdered()
where city.Population > 10000
select city)
.Take(1000);
var plinqQuery = table
.AsParallel()
.Where(n => Enumerable.Range(2, (int) Math.Sqrt(n.Item1)).All(i => n.Item1 % i > 0))
.Take(10)
.ToList();
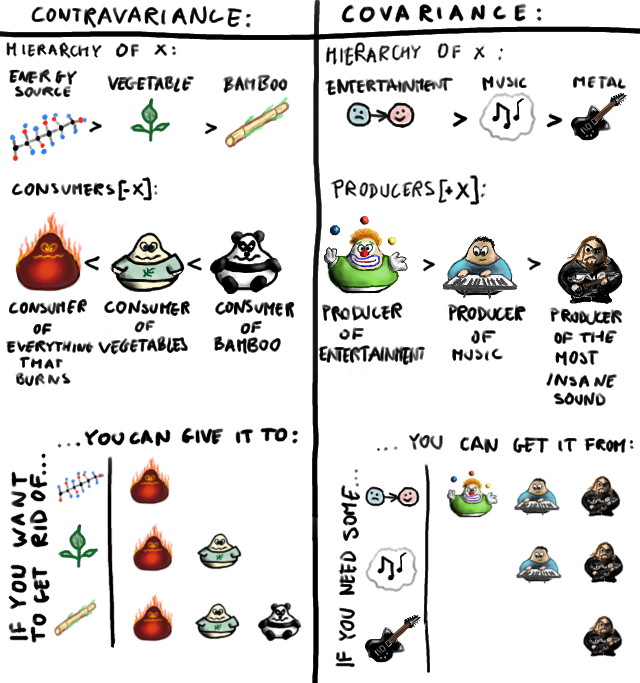
2. Covariance – it preserves the ordering of types. Given delegate as an example, we can assign functions to delegate that return type defined by delegate or any type that is derived from that type. Example: if delegate returns a Person, we can assigned function that returns more ‘specific’ type such as Student (given Student :> Person);
3. Contravariance – it reverses the ordering of types. Again using delegates as example we can assign function to delegate which takes the same type of parameters or parameters that derive from the base type.
Pardon that vague definition that only applies to the very basic example of programming. The main difference is if the function is an ‘in’ or ‘out’ function. There’s also some nuances when using mutable or nonmutable collections and much more. I recommend reading this article.
4. Multicasting – it’s the ability of a delegate to register multiple methods to it. Then, when the multicast delegate is called, it invokes the delegates in the list, in order. Only delegates of the same type can be combined. We can add and remove the subscriptions using ‘+’ and ‘-‘ characters. The idea is used in the observer pattern, among other.
5. Threads – SuppressFlow – stops the propagation of parent thread access rights to children threads. Basically, if we create a new Thread it inherits access rights from the thread it was created in. To stop it, we can execute the SuppresFlow command on the execution context.
6. Threads – SuppressFinalize – marks object as finalized or in other words removes it from the garbage collector finalization queue.
7. Func vs Action – Func is a shorthand for a delegate with a return value. Action is simply a delegate that has no return value (void).
8. Closure – is a function that is bound to the environment in which it is declared. It preserves the variable declared in its scope, even if they go out of it. This means the closure actually extends their in-memory lifetime to match the longest living delegate they’re used in.
9. Error handling – throw() – doesn’t modify the call stack, can be used to rethrow exceptions, while throw(e) resets the call stack. Additionally exceptions can be rethrown with additional exception like this:
catch (Exception ex)
{
throw new Exception("hi mate!", ex);
}10. Structures are value types, with all the value type consequences (lower memory usage, passed by value etc.).
11. Short-circuiting – it happens during the usage of logic operators (and, or, xor). While short-circuiting, if the first condition fails, the rest is skipped. To use short-circuting just use the double operator like && instead of & or || instead of |.
12. Law of demeter – in regard to methods, choosing the method signature that will create the minimally coupled arguments.
13. Non static class can include static fields and methods, while class declared as static can include ONLY static fields, methods and properties. One interesting note about static elements is that the static field variable initializers of a class declaration correspond to a sequence of assignments that are executed in the textual order in which they appear in the class declaration. If a static constructor exists in the class, execution of the static field initializers occurs immediately prior to executing that static constructor. Otherwise, the static field initializers are executed at an implementation-dependent time prior to the first use of a static field of that class. This means that a static property shoudn’t refer to the other property or field that is declared after the first one. In such case, the first one will receive a null, because the later one isn’t yet initialized.
14. Extension methods are declared static.
15. Sealed keyword prevents inheritance.
16. Virtual methods can be overriden in an inherited class. Without the virtual modifier it cannot be done, but a ‘new’ modifier can be used to shadow the base method. This can sometimes create a strange behaviour, for example if the variable was previously assigned to a base class and is reassigned to a derived class. Execution of shadowed method would still point to the one from base class.
17. Generics (eg. List<string>) – one of the main advantage of generics is avoiding boxing operations on value types. There is a performance overhead to boxing and unboxing operations (putting object from stack to heam and adding a reference to it on the stack).
18. We cannot use the ‘as’ operator for the value types, because it returns null if casting is impossible, which is not possible for value types. We should use explicit casting or TryParse.
19. Casting – ‘is’ checks type and returns true/false, while ‘as’ returns the type<T> or null.
20. Dynamic keyword prevents static type checking.
21. Default property/method access modified is ‘private’.
21. Properties add accessors to fields.
22. Both classes and structs can implement an interface.
23. Icomparable – for sorting, has to create a method that returns -1,0,1 for comparing, uses the compareTo() method.
24. IComparator – used for creating a custom comparisons, uses the Compare() method.
25. IEnumerable – used for iteration of collections, provied an GetEnumerator() method.
26. Yield – provides a handler for lazy loading of collection elements; side effect: creates a state machine which keeps track of the MoveNext nd Current elements, used for enumerations.
27. IDisposable – provides Dispose() method, used in unmanaged code to clear item from memory.
28. Garbage collector frees the objects from the heap. The stack is cleared at the end of method execution.
29. ‘using’ is a wrapper around Dispose() method of the object with IDisposable interface used in the try/catch/finally blocks.
30. Finalizer is called by garbage collector.
31. Dispose can be called from code directly.
32. Weak Reference – kind of caching mechanism for garbage collection. Marks the entity as collectible.
33. String is a reference type that acts like a value type. It’s immutable, has overloaded comparison operation to compare on object value, not reference address.
34. String interning – is a process of addressing different string variables to the same object in memory on the heap.
35. IFormattable – used to convert object properties to string and vice-versa.
36. Parse vs Convert – parse takes string as argument and can throw ArgumentNullException. Convert can take other base values, doesn’t throw when passed NULL, instead returns type default value.
37. Strong-named assembly – is signed with a public/private key and digital signature. Advantages: guarantess uniqueness, source, offers integrity check based on the hashsum; disadvantages: can reference only other strong-signed assemblies.
38. Delayed-partial signing – signing with public key and delaying the final signing with a private key.
39. Global Assembly Cache (GAC) – shares resources on the entire machine, used to share assemblies between applications.
40. Performance counters – are unmanaged code, can be viewed in the performance monitor (perfmon.exe), implement IDisposable interface.
41. Database connectino pooling – gathering/checking if a connection to a given db is already opened. If so, using that connection instead of creating a new one.